I know that everyone runs the Lync Best Practices Analyzer (BPA) on a regular basis…right? After running the BPA, you might see the following warning:
Pool fully qualified domain name (FQDN) “fqdn” is not found as a http service principal name (SPN) on any user or computer. Kerberos web authentication is not configured..
The warning pops up due to the fact that Lync uses NetworkService to run the Web Services and NetworkService cannot have SPNs assigned to it (this is a change from how OCS handled it).
I am not going to address the “why use kerberos authentication?” because there is already a great article written by Jens Trier Rasmussen. I suggest reading it before proceeding.
The rest of this post will describe the process of enabling Kerberos authentication for the Lync Web Services.
1) Create a Kerberos account
Pre-req: member of Domain Admins and computer running Lync Management Shell (LMS)
From the LMS, run: New-CsKerberosAccount –UserAccount “Domain\UserAccount” –ContainerDN “CN=Users,DC=DomainName,DC=DomainExtenstion”
My command: New-CsKerberosAccount –UserAccount “Homelab\LyncKerbAcct” –ContainerDN “OU=UC Objects,DC=homelab,DC=local”
Note that the –UserAccount parameter is used even though we are creating a computer account with this command.
2) Assign the Kerberos account to a site
Pre-req: member of RTCUniversalServerAdmins and computer running Lync Management Shell (LMS)
To use the Kerberos account, you must assign it to a site. While you can create multiple Kerberos accounts for your environment, you can only assign one account per Lync site.
From the LMS run: New-CsKerberosAccountAssignment –UserAccount “Domain\UserAccount” –Identity “site:SiteName”
My command: New-CsKerberosAccountAssignment –UserAccount “Homelab\LyncKerbAcct” –Identity “site:Datacenter”
Then run Enable-CsTopology
3) Set Kerberos account password and Synchronize to IIS
Pre-req: member of RTCUniversalServerAdmins and computer running Lync Management Shell (LMS)
From the LMS run: Set-CsKerberosAccountPassword –UserAccount “Domain\UserAccount”
My command: Set-CsKerberosAccountPassword –UserAccount “Homelab\LyncKerbAcct”
If any servers are added to the topology in the site (like Front-ends and Directors) you will need to synchronize the Kerberos account password to IIS of the new server.
From LMS run: Set-CsKerberosAccountPassword –FromComputer SourceComputer –ToComputer DestinationComputer
My command: Set-CsKerberosAccountPassword –FromComputer lablyncfe01.homelab.local –ToComputer lablyncfe02.homelab.local
4) Testing to make sure Kerberos is working properly
To test for full functional readiness of Kerberos within a site, the following command can be run to create a report:
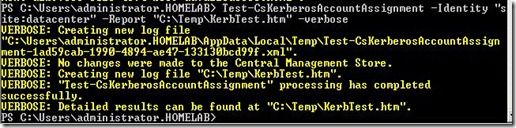
From LMS run: Test-CsKerberosAccountAssignment –Identity “site:SiteName” –Report “C:\reportpath\reportname.htm” –Verbose
My command: Test-CsKerberosAccountAssignment –Identity “site:Datacenter” –Report “C:\Temp\KerbTest.htm”
Report generated:
Hope this helps!







Great guide, thanks!
ReplyDeleteJust FYI, I have many Lync servers, so I skipped Step 3. And the test failed. After more reading, I found enable-cstopology will force that same sync to all Lync servers.
ReplyDeletedo you have to do this? I have existing system that works fine, do l still need to do this? will the procedure change if l have to do this for existing system?
ReplyDeleteThis is not required and your implementation will work fine without it. Kerberos auth is more efficient and considered best practice.
DeleteA further heads up..I was having trouble connecting to the Control Panel (The URL worked fine) as well as getting the "Credentials are Required" box on many users. Manually typing the creds didnt work.
ReplyDeleteFinally found that an over zelous Administrator had deleted my Lync Kerberos Account.
Thanks for the process of re-adding the account!
Thanks, Tim!
ReplyDeleteIt's very useful article!
Unser Unternehmen bietet beste Qualität und Web-Entwicklung Dienstleistungen in Deutschland. Wir bieten derzeit Web und mobile Anwendung Entwicklungsdienstleistungen .http://www.accuratesolutionsltd.com/web-entwicklung/
ReplyDeletelouis vuitton outlet
ReplyDeletecheap jordans
kate spade handbags
michael kors outlet
christian louboutin shoes
coach factorty outlet
kate spade outlet
christian louboutin shoes
michael kors bags
ray ban outlet
kobe bryant shoes
replica watches
replica watches
oakley sunglasses
true religion jeans
coach factory outlet
jordan 3
hollister clothing
adidas originals
caoch outlet
tory burch sale
coach outlet
cheap ray ban sunglasses
nike nfl jerseys
michael kors handbags
michael kors handbags
michael kors purses
oakley sunglasses wholesale
nike roshe run
coach outlet store online
michael kors handbags
pandora jewelry
hollister clothing
air jordan 13
adidas superstar
coach factorty outlet
kobe shoes 11
gucci handbags
cheap jordans
hollister outlet
20164.14wengdongdong
Ihr Blog ist sehr interessant, ich lese jeden Artikel und ich es gefällt mir wirklich! Vielen Dank, ich für neue Artikel und Tipps warten.
ReplyDeleteVielen Dank, dass Sie Ihre wichtigen Informationen für diese Blogs weitergeben. Ihr Vorschlag ist vollkommen richtig, Kliff Technologies bietet Webentwicklung in Deutschland Dienstleistungen an.
ReplyDeletegta 5 ios apk obb
ReplyDeletegta 5 android requirements
GTA 5 200 MB
A good website is useful.
ReplyDeleteลิเวอร์พูล
ข่าวอาร์เซนอล
Hi...
ReplyDeleteWhen a client has authenticated to the server (Kerberos or NTLM) it gets a ... This setting is a part of the web services configuration.
You are also read more Business Loan Interest Rates
Sonic’s menu includes the most traditional aspects of fast-food cuisine: hot dogs, chilli dogs,
ReplyDeleteonion rings, soft drinks, slushies, milkshakes, hamburgers, french fries, corn dogs,
sundaes and banana splits.
They have continuously updated their fast food menu to satisfy their customers’ requirements.
Sonic Menu with Prices
Thanks for the well-researched article—it really clarified things! Here’s another article you might find useful Reaction Time Test. Reaction time tests can show how mindfulness exercises improve focus and response time.
ReplyDelete