I have seen this situation/question come up over and over again so I decided to write a blog post on it. The question: “How do I configure Exchange to receive email from the Internet or from a MFP scanner? You might think this is pretty straight forward, but I have seen this misconfigured over and over.
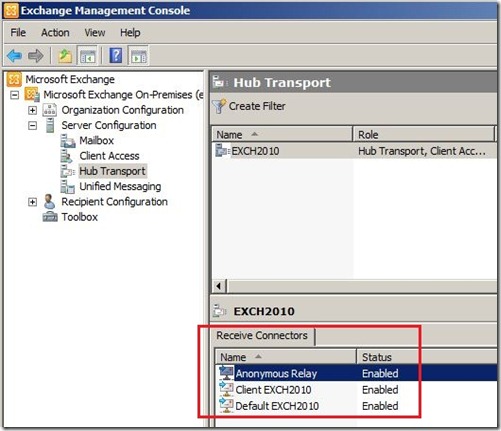
Exchange 2007/2010 comes with two default receive connectors installed per HUB Transport server: “Default Servername” and “Client Servername”. The “Default Servername” connector is used for all connections from other HUB or Edge Transport servers in the organization. The “Client Servername” connector is used for all SMTP connections from all non-MAPI clients, such as POP or IMAP. This is the default view for every HUB Transport server.
Most likely a connector from the Internet or a MFP scanner will need to connect to Exchange via SMTP as an anonymous user or with basic authentication. Let’s discuss anonymous connections. I have seen other posts instruct administrators to allow anonymous connectivity through the “Default Servername” receive connector. My advise: Leave the two default receive connectors alone and add a new receive connector to manage all anonymous connectivity and all non-default connectivity. Allowing anonymous relay is a security risk and should be controlled if needed. By creating a separate receive connector I get a warm fuzzy because I have segmented off all non-default traffic to its own connector and I can create a whitelist of IP addresses that are allowed to use it.
So, let’s get started… In EMC, navigate to the Server Configuration –> Hub Transport node and select New Receive Connector in the Action pane. This will open the New Receive Connector wizard. Let’s name the connector “Anonymous Relay” and select Custom from the drop down.
On the Remote Network Settings page, delete the default all-inclusive IP range and add the IP addresses that you want the connector to allow connectivity. We will add our MFP scanner and our hosted SPAM/Hygiene service. Note that you can also add IP ranges and whole subnets.


New-ReceiveConnector –Name “Anonymous Relay” –Usage Custom –PermissionGroups AnonymousUsers –Bindings ‘0.0.0.0:25’ –RemoteIpRanges ‘10.1.1.250’,’10.2.2.2-10.2.2.100’.’74.2.2.2’

Get-ReceiveConnector “Anonymous Relay” | Add-ADPermission –User “NT AUTHORITY\ANONYMOUS LOGON” –ExtendedRights “Ms-Exch-SMTP-Accept-Any-Recipient”
All done, now we have created a specific receive connector for anonymous relay and can control what devices are allowed to use it.


ReplyDeleteIP scan 2.2.1
fastest and good scanner for ever just put IP range which thing u want its scan and give u result
http://bicombusiness.blogspot.com/2016/01/ip-scan-221.html
prada shoes outlet
ReplyDeletecheap jerseys for sale
ugg australia
cheap ugg boots
michael kors outlet clearance
cheap oakley sunglasses
nike shoes
louboutin shoes
sac louis vuitton
air jordan shoes
nike outlet store
ReplyDeleteralph lauren outlet
bottega verde sito ufficiale
michael kors outlet
kansas city chiefs jerseys
canada goose jackets
air jordans
louboutin shoes
coach outlet
skechers outlet
Using Anonymous Proxy is a must if you are concerned about your privacy on the internet. To surf on the net safely and securely to protect your sensitive financial and personal data you need to use Anonymous Proxy. Anonymous
ReplyDeleteThanks for sharing this information. I really like your blog post very much. You have really shared a informative and interesting blog post with people.. exchanger24
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThe QuickBooks Connection Diagnostic Tool is designed to troubleshoot networking and multi-person mistakes that could arise whilst you open an employer file. If you’re experiencing H202, H505, or 6000 collection mistakes, this device can help. The Quickbooks diagnostic connection tool works best with computer systems going for walks Microsoft Windows 7, Windows Vista, or Windows XP with QuickBooks 2008 and more recent or QuickBooks Enterprise Solutions 8. zero and more recent.
ReplyDeleteNice information, valuable and excellent design, as share good stuff with good ideas and concepts, lots of great information and inspiration, both of which I need, thanks to offer such a helpful information here. Microsoft365
ReplyDeleteHi....
ReplyDeleteHow to create a secure Receive Connector on an Exchange Server 2010 Hub Transport server for anonymous email relay.
You are also read more 100 Home Loan
This is my first time visit here. From the tons of comments on your articles,I guess I am not only one having all the enjoyment right here! shift windows s not working windows 11
ReplyDeleteRead your post and find it interesting. We look forward to reading your post soon. Best wishes to you with future updates. Thanks for this informative article. Visit their website for more information. See my article if you want to create tips and tricks for your own business. Please enter your comment article after reading your article. We appreciate your submission. Kohi Click Test - Best CPS Test!
ReplyDeleteThank You and I have a super present: What Do House Renovations Cost home remodel
ReplyDeleteSpray tan at home brings the luxury of a professional sun-kissed glow directly to your door. Expert technicians provide a customized, streak-free tan tailored to your skin tone, using high-quality products for a flawless finish. Perfect for busy schedules or those who prefer the comfort of their own space, spray tan at home offers a convenient, UV-free alternative for a radiant, natural-looking tan.
ReplyDeleteGet beautiful, voluminous lashes at affordable prices in Brooklyn. Enjoy professional eyelash extension services with high-quality materials, tailored to your desired look, all while staying within your budget. Perfect for a stunning, long-lasting lash enhancement!
ReplyDeleteBronzed by Julie provides mobile, organic spray tanning and teeth whitening services. Natural and organic ingredients for best results.
ReplyDeleteSpray Tan Solutions NYC
Appreciate you sharing, it is great article. Many thanks again. Bedbug Control Pharr Awesome.
ReplyDeleteAppreciate you sharing, it is great article. Many thanks again. Pest Control Weslaco Awesome.
ReplyDeleteI enjoy it for creating the details, keep up the truly amazing performance continuing new kitchen renovation Honolulu.
ReplyDeleteBronzed By Julie is a professional mobile organic spray tanning, and teeth whitening service in New York City. Let us make you feel more confident and beautiful with our custom tans and brilliant teeth whitening options at your home,<a href="https://thegeneralpost.com/organic-spray-tan-services-a-safe-and-natural-glow/>Organic spray tan services</a>
ReplyDeletebgrjj473hd
ReplyDeletegolden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet